Solana Founder AI Threat to Crypto: Yakovenko Warns Quantum Defenses May Fall First
The Solana founder AI threat to crypto refers to Anatoly Yakovenko’s warning that artificial intelligence — not quantum computers — poses the most immediate danger to the cryptography securing blockchain wallets. Anatoly Yakovenko just put a new villain on the board. AI, he says, not some future quantum machine, is the thing most likely to crack the cryptography sitting under every wallet today. That cuts hard against a year of industry messaging that framed post-quantum cryptography (PQC) as the safe long-term answer. If he’s right, the clock for hardening Bitcoin, Ethereum, and Solana wallets is far shorter than what most investors are pricing in. And the L2 ecosystem on Ethereum is the most exposed piece of the board.
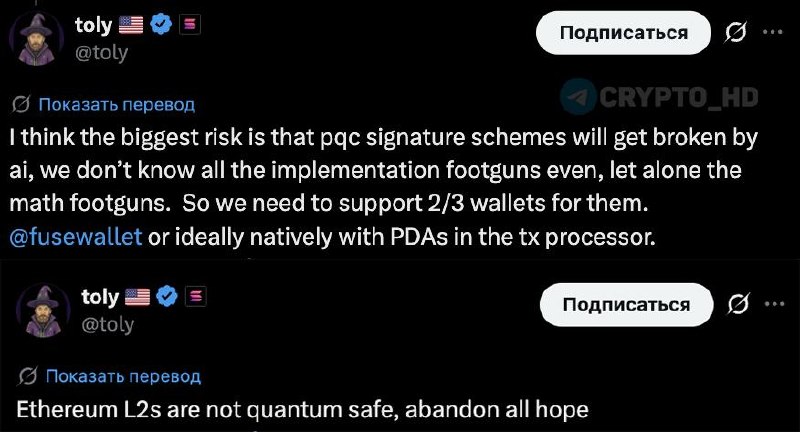
The warning lands at a sensitive moment. For the past 18 months, builders have been pivoting toward PQC signature schemes as the default migration path. Ethereum L2 teams, exchanges, even custody providers — all signalling that quantum-resistant signatures will be the next big infrastructure upgrade. Yakovenko’s claim is blunt: those schemes can be broken — or at least probed for weaknesses — by AI faster than human researchers can patch them. That changes the math for any treasury holding ETH, SOL, or BTC in long-tail addresses.
His core point is technical but the consequence is financial. Post-quantum signature algorithms rely on mathematical assumptions that are still relatively young compared to elliptic-curve cryptography, which has been pounded on by academia for forty years. Yakovenko argues two things are not yet fully understood: implementation bugs in real PQC code, and possible structural weaknesses in the underlying math itself. AI tooling, in his framing, is good at exactly the kind of pattern hunting that surfaces both. Worse, it scales. One researcher with the right model can probe a scheme far faster than the small global pool of cryptographers can audit it. Think of it as one person with a metal detector versus a thousand people with metal detectors — except the thousand are running 24/7 and never get tired.
That asymmetry is the real story. Crypto’s security model has always assumed the defender community is at least as fast as the attacker community. AI flips that. A vulnerability discovered by an automated agent in an obscure PQC library could propagate to dozens of forks before maintainers even open the issue. For chains that are mid-migration — and that’s most of them — the window between “AI finds the flaw” and “exploit ships” may be measured in days, not the comfortable months protocol teams have planned around.
Yakovenko’s proposed defenses are pragmatic rather than theoretical. Multisig wallets are the near-term hedge, on the simple logic that an attacker has to break multiple keys instead of one. It’s the same reason banks use two-key safe deposit boxes — one bad actor with one key gets nowhere. The deeper fix, in his view, is protocol-level. Here he flags Solana’s Program Derived Addresses (PDAs) as an example of how key control can be moved into program logic instead of sitting in a single signature. Notably, he says Ethereum’s L2 ecosystem is not ready for the quantum threat. That reads as a direct shot at the rollup-heavy roadmap ETH-aligned builders have committed to.
He also isn’t speaking into a vacuum. The industry has been edging toward this conversation for months. Theoretical computer scientist Scott Aaronson has been arguing that quantum readiness is an alarm worth raising publicly. There has already been a documented test-style break of a weakened cryptographic target by quantum hardware. Google’s research arm has been saying the cryptography refresh cycle needs to start now, not later. Yakovenko’s contribution is to push the threat actor from “future quantum machine” to “AI agent available today” — and that reframes who is at risk and how soon.
The macro angle is straightforward: this is a risk-asset story, not just a security story. Crypto trades on confidence in the underlying primitives. Any credible signal that wallet-level security is on a shorter clock than markets believe puts pressure on long-duration crypto theses — the kind of “hold for five years” allocations institutional buyers have been making in BTC and ETH through spot ETFs. If a sitting founder of a top-five chain by market cap is saying L2 security is not quantum-ready, allocators will read that as a discount factor on ETH-beta exposure specifically. SOL, by contrast, gets a relative narrative tailwind from Yakovenko positioning PDAs as part of the answer — even if that’s self-serving framing.
The adoption-signal angle is where this gets uncomfortable for the ETH ecosystem. Ethereum’s entire scaling story for 2025-2026 has been routed through L2s — Arbitrum, Optimism, Base, zkSync, Linea, and the long tail of app-chains. If those rollups are, as Yakovenko claims, behind on quantum-and-AI-resistant signature design, then the locked value sitting in their bridges and contracts is the most concentrated soft target in crypto. That’s not a price call for tomorrow. It’s a structural overhang on the multi-year bull case the L2 thesis has been built on. It also hands custodians, treasuries, and ETF issuers a new question to ask their counterparties: what’s your PQC migration plan, and is it AI-audited?
There’s a quieter regulation angle worth flagging too. U.S. and EU regulators have been moving toward formal PQC migration mandates for financial infrastructure. If AI-driven vulnerability discovery becomes the dominant threat model — instead of the slower quantum-hardware threat regulators have been planning around — the rulebooks already in draft may be obsolete before they ship. It’s a bit like writing earthquake codes for a region where the actual risk turns out to be flooding. Exchanges and custodians operating under frameworks like MiCA or the U.S. money-transmitter regime could find themselves compliant on paper and exposed in practice. That’s the kind of mismatch that historically triggers emergency guidance, not orderly migration.
Worth noting: Yakovenko did not give a timeline, did not name specific PQC schemes as already broken, and did not claim any chain has been compromised. This is a warning shot, not a disclosure. But his track record of calling infrastructure issues early — Solana’s own outage history forced him into hard public positions on validator design and fee markets — means his security calls tend to get taken seriously by builders even when traders shrug them off in the short term.
What this means
The bottom line: crypto’s security migration is now a two-front problem, with AI-driven cryptanalysis emerging as a faster threat than quantum hardware. The signal here is that crypto’s security migration is now a two-front problem. The industry has been preparing for quantum computers as the eventual breaker of today’s elliptic-curve signatures. Yakovenko is saying the more pressing breaker is AI, hunting for cracks in the very PQC schemes meant to replace them. For ETH and the L2 ecosystem, that’s the most direct exposure he names. Bridges, rollup sequencers, and any contract relying on a single-key signing model become the first places allocators will stress-test. For SOL, the framing is opportunistic but defensible: PDAs and program-controlled accounts move some of the attack surface away from raw signatures, which is exactly the architectural argument Solana has been making for years. Multisig adoption — Safe-style smart accounts on Ethereum, native multisig on Bitcoin via Taproot, Squads on Solana — becomes the cheap, immediate hedge any serious treasury can deploy this quarter.
What to watch next is concrete. First, response from Ethereum core devs and major L2 teams (Arbitrum, Optimism, Base, zkSync) — silence will be read as confirmation of Yakovenko’s “not ready” framing, while a public PQC + AI-audit roadmap will defuse it. Second, custody providers and ETF issuers — Coinbase Custody, BitGo, Fidelity Digital Assets — and whether they update disclosures around signature-scheme risk. Third, any near-term move from NIST or ENISA on accelerating PQC standards in light of AI-assisted cryptanalysis; that’s the regulatory tripwire. And fourth, on-chain: watch flows into multisig contracts on Ethereum and Solana in the coming weeks. A spike in Safe deployments or Squads adoption would be the clearest market-level signal that holders took Yakovenko at his word — and the cleanest leading indicator that this warning is repricing risk rather than just generating headlines.